آسیبپذیریهای حیاتی هفته دوم اردیبهشتماه

این هفته در محصولات بسیار مهم Cisco چندین آسیبپذیری با سطح خطر «حیاتی» و «بالا» شناسایی شده است. همچنین محصولات پرکاربرد شرکتهای Apache ، Avira ، VMware و Mozilla (از جمله مروگر محبوب Firefox) نیز چندین آسیبپذیری حیاتی داشتند. کرنل لینوکس و WordPress نیز آسیبپذیریهایی با سطح خطر «بالا» داشتند.
|
نوع آسیبپذیری |
محصول آسیبپذیر |
شناسه آسیبپذیری |
|
Weak Authentication |
ABB MicroSCADA Pro SYS600 |
CVE-2019-5620 |
|
Privilege Escalation |
ABB Product Central Licensing Server |
CVE-2020-8471 |
|
Denial of Service |
ABB Products Central Licensing Server |
CVE-2020-8475 |
|
Privilege Escalation |
ABB Products Central Licensing Server |
CVE-2020-8476 |
|
XML External Entity |
ABB Products Central Licensing Server |
CVE-2020-8479 |
|
Privilege Escalation |
ABB Products System Extensions |
CVE-2020-8481 |
|
Privilege Escalation |
ABB System 800xA Base Folder Permission |
CVE-2020-8473 |
|
Privilege Escalation |
ABB System 800xA Base Inter-Process Communication |
CVE-2020-8487 |
|
Privilege Escalation |
ABB System 800xA Batch Management Inter-Process Communication |
CVE-2020-8488 |
|
Privilege Escalation |
ABB System 800xA for DCI Inter-Process Communication |
CVE-2020-8484 |
|
Privilege Escalation |
ABB System 800xA for MOD 300 Inter-Process Communication |
CVE-2020-8485 |
|
Privilege Escalation |
ABB System 800xA Information Management Inter-Process Communication |
CVE-2020-8489 |
|
Privilege Escalation |
ABB System 800xA OPC Server for AC800M Folder Permission |
CVE-2020-8472 |
|
Privilege Escalation |
ABB System 800xA OPC Server for AC800M Inter-Process Communication |
CVE-2020-8478 |
|
Privilege Escalation |
ABB System 800xA RNRP Inter-Process Communication |
CVE-2020-8486 |
|
Memory Corruption |
ABBS Software Audio Media Player Stack-based |
CVE-2019-5621 |
|
Command Injection |
Accellion File Transfer Appliance |
CVE-2019-5623 |
|
Weak Authentication |
Accellion File Transfer Appliance Default Credentials |
CVE-2019-5622 |
|
Information Disclosure |
Advanced Woo Search Plugin class-aws-search.php |
CVE-2020-12070 |
|
XSS |
AirDisk Pro App |
CVE-2020-12131 |
|
XSS |
AirDisk Pro App |
CVE-2020-12130 |
|
XSS |
AirDisk Pro App |
CVE-2020-12129 |
|
Privilege Escalation |
AMD ATI atillk64.sys |
CVE-2020-12138 |
|
Directory Traversal |
ansible-engine Archive |
CVE-2020-10691 |
|
Denial of Service |
Apache ATS HTTP2 |
CVE-2020-9481 |
|
Remote Code Execution |
Apache IoTDB JMX Service |
CVE-2020-1952 |
|
Weak Encryption |
Apache Log4j SMTP Appender SMTPS Man-in-the-Middle |
CVE-2020-9488 |
|
CSRF |
Apache OFBiz |
CVE-2019-0235 |
|
Privilege Escalation |
Apache OFBiz Injection |
CVE-2019-12425 |
|
Memory Corruption |
Artifex jbig2dec jbig2_image.c jbig2_image_compose |
CVE-2020-12268 |
|
Privilege Escalation |
Avira Antivirus Symlink |
CVE-2020-12254 |
|
Directory Traversal |
B&R Automation Studio SharpZipLib |
CVE-2019-19102 |
|
Weak Authentication |
B&R Automation Studio TLS Validation |
CVE-2019-19101 |
|
Privilege Escalation |
B&R Automation Studio Upgrade Service |
CVE-2019-19100 |
|
Memory Corruption |
BMC Control-M/Agent Email |
CVE-2019-19215 |
|
Privilege Escalation |
BMC Control-M/Agent File Copy |
CVE-2019-19216 |
|
Information Disclosure |
BMC Control-M/Agent File Download |
CVE-2019-19219 |
|
Privilege Escalation |
BMC Control-M/Agent OS |
CVE-2019-19220 |
|
Privilege Escalation |
BMC Control-M/Agent OS |
CVE-2019-19217 |
|
unknown vulnerability |
BMC Control-M/Agent Password Storage |
CVE-2019-19218 |
|
Denial of Service |
Cerner Medico |
CVE-2020-11674 |
|
Memory Corruption |
Cerner Medico |
CVE-2020-11677 |
|
Memory Corruption |
Cerner Medico |
CVE-2020-11676 |
|
Memory Corruption |
Cerner Medico |
CVE-2020-11675 |
|
CSRF |
Cisco IOS and Cisco IOS XE Software Web UI |
CVE-2019-16009 |
|
Privilege Escalation |
Cisco IOS XE SD-WAN CLI |
CVE-2019-16011 |
|
Buffer Overflow |
Cisco IP Phones Web Application |
CVE-2016-1421 |
|
Remote Code Execution and Denial of Service |
Cisco IP Phones Web Server |
CVE-2020-3161 |
|
CSRF |
Cisco Mobility Express Software |
CVE-2020-3261 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3239 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3240 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3243 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3247 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3248 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3249 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3250 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3251 |
|
Multiple Vulnerabilities |
Cisco UCS Director and Cisco UCS Director Express |
CVE-2020-3252 |
|
Code Execution |
Cisco Webex Network Recording Player and Cisco Webex Player |
CVE-2020-3194 |
|
Information Disclosure |
Cisco Wi-Fi Protected Network and Wi-Fi Protected Network 2 |
CVE-2019-15126 |
|
Denial of Service |
Cisco Wireless LAN Controller 802.11 Generic Advertisement Service |
CVE-2020-3273 |
|
Denial of Service |
Cisco Wireless LAN Controller CAPWAP |
CVE-2020-3262 |
|
XSS |
Cybozu Garoon Email Application |
CVE-2020-5564 |
|
Privilege Escalation |
Cybozu Garoon E-mail/Messages |
CVE-2020-5566 |
|
XSS |
Cybozu Garoon Messages/Bulletin Board |
CVE-2020-5568 |
|
Server-Side Request Forgery |
Cybozu Garoon V-CUBE Meeting |
CVE-2020-5562 |
|
Privilege Escalation |
Cybozu Garoon Workflow/MultiReport |
CVE-2020-5565 |
|
Directory Traversal |
decompress Package Archive Symlink |
CVE-2020-12265 |
|
Privilege Escalation |
Electron Cash SLP Edition Mint Tool |
CVE-2020-11014 |
|
Privilege Escalation |
ESET Antivirus/Antispyware Module Module |
CVE-2020-11446 |
|
XSS |
F5 BIG-IP APM APM Portal Access Reflected |
CVE-2020-5889 |
|
Denial of Service |
F5 BIG-IP APM Traffic Management Microkernel |
CVE-2020-5874 |
|
Information Disclosure |
F5 BIG-IP APM/Edge Gateway/FirePass Edge Client |
CVE-2020-5892 |
|
Weak Encryption |
F5 BIG-IP ASM SSL Profile |
CVE-2020-5879 |
|
Denial of Service |
F5 BIG-IP Backend Server |
CVE-2020-5871 |
|
Weak Encryption |
F5 BIG-IP Edge Client VPN |
CVE-2020-5893 |
|
unknown vulnerability |
F5 BIG-IP High Availability |
CVE-2020-5886 |
|
unknown vulnerability |
F5 BIG-IP High Availability |
CVE-2020-5885 |
|
unknown vulnerability |
F5 BIG-IP High Availability |
CVE-2020-5884 |
|
Denial of Service |
F5 BIG-IP HTTP2 |
CVE-2020-5891 |
|
Denial of Service |
F5 BIG-IP iRule Memory Leak |
CVE-2020-5883 |
|
Denial of Service |
F5 BIG-IP iRules Command tcp |
CVE-2020-5877 |
|
Privilege Escalation |
F5 BIG-IP restjavad File Upload |
CVE-2020-5880 |
|
Denial of Service |
F5 BIG-IP Traffic Management Microkernel |
CVE-2020-5882 |
|
Denial of Service |
F5 BIG-IP Traffic Management Microkernel |
CVE-2020-5872 |
|
Privilege Escalation |
F5 BIG-IP Traffic Management Microkernel |
CVE-2020-5876 |
|
Denial of Service |
F5 BIG-IP Traffic Management Microkernel Restart |
CVE-2020-5878 |
|
Denial of Service |
F5 BIG-IP Traffic Management Microkernel Restart |
CVE-2020-5875 |
|
Privilege Escalation |
F5 BIG-IP Virtual Edition |
CVE-2020-5888 |
|
Denial of Service |
F5 BIG-IP Virtual Edition VLAN Group |
CVE-2020-5881 |
|
Privilege Escalation |
F5 BIG-IP/BIG-IP Virtual Edition |
CVE-2020-5887 |
|
Information Disclosure |
F5 BIG-IP/BIG-IQ Administrative Interface |
CVE-2020-5890 |
|
Privilege Escalation |
F5 BIG-IP/BIG-IQ scp |
CVE-2020-5873 |
|
Weak Authentication |
F5 BIG-IQ High Availability |
CVE-2020-5870 |
|
Weak Encryption |
F5 BIG-IQ High Availability |
CVE-2020-5869 |
|
Privilege Escalation |
F5 BIG-IQ User Interface |
CVE-2020-5868 |
|
Weak Authentication |
Faye |
CVE-2020-11020 |
|
Weak Authentication |
Fortinet FortiMail/FortiVoiceEntreprise Password Change |
CVE-2020-9294 |
|
Information Disclosure |
FreeBSD Configuration Kernel Memory |
CVE-2020-7453 |
|
Memory Corruption |
FreeBSD epair Virtual Network Module |
CVE-2020-7452 |
|
Privilege Escalation |
FreeBSD ioctl Command |
CVE-2019-15877 |
|
Privilege Escalation |
FreeBSD ioctl Command |
CVE-2019-15876 |
|
Memory Corruption |
FreeBSD |
CVE-2019-15874 |
|
Memory Corruption |
FreeBSD Out-of-Bounds |
CVE-2019-5614 |
|
Information Disclosure |
FreeBSD TCP SYN-ACK Kernel Memory |
CVE-2020-7451 |
|
Privilege Escalation |
G.SKILL Trident Z Lighting Control ene.sys |
CVE-2020-12446 |
|
Privilege Escalation |
Genius Bytes Genius Server Application Plugin |
CVE-2019-16653 |
|
Privilege Escalation |
Genius Bytes Genius Server |
CVE-2019-16652 |
|
Remote Code Execution |
Gigamon GigaVUE File Upload |
CVE-2020-12252 |
|
Information Disclosure |
Gigamon GigaVUE Upload |
CVE-2020-12251 |
|
Privilege Escalation |
GitLab API |
CVE-2020-12275 |
|
Privilege Escalation |
GitLab Mirror |
CVE-2020-12277 |
|
XSS |
GitLab Notification Stored |
CVE-2020-12276 |
|
Memory Corruption |
GNU C Library Tilde Expansion Use-After-Free |
CVE-2020-1752 |
|
XSS |
GNU Mailman MIME Part |
CVE-2020-12137 |
|
XSS |
Grafana Annotation Popup |
CVE-2020-12052 |
|
XSS |
Grafana |
CVE-2020-12245 |
|
Information Disclosure |
Grafana grafana |
CVE-2020-12458 |
|
Information Disclosure |
Grafana grafana.ini |
CVE-2020-12459 |
|
Open Redirect |
HCL Connections |
CVE-2019-4209 |
|
Memory Corruption |
HPE Blade Maintenance Entity Service Port 17185 |
CVE-2020-7131 |
|
Privilege Escalation |
HPE IOT/GCP Access |
CVE-2020-7134 |
|
Privilege Escalation |
HPE IOT/GCP |
CVE-2020-7133 |
|
Code Execution |
HPE Server |
CVE-2020-7135 |
|
Privilege Escalation |
HPE Service Pack for ProLiant |
CVE-2020-7136 |
|
Privilege Escalation |
Huawei AR3200 |
CVE-2020-9068 |
|
Memory Corruption |
Huawei Honor V10 Driver Out-of-Bounds |
CVE-2020-1806 |
|
Memory Corruption |
Huawei Honor V10 Driver Out-of-Bounds |
CVE-2020-1805 |
|
Memory Corruption |
Huawei Honor V10 Driver Out-of-Bounds |
CVE-2020-1804 |
|
Denial of Service |
Huawei Lion-AL00C |
CVE-2020-1880 |
|
Privilege Escalation |
Huawei Mate 20 adb |
CVE-2020-1807 |
|
Memory Corruption |
Huawei OceanStor 5310 |
CVE-2020-9098 |
|
Privilege Escalation |
Huawei OSD |
CVE-2020-9072 |
|
Privilege Escalation |
Huawei PCManager |
CVE-2020-1817 |
|
Privilege Escalation |
Huawei PCManager |
CVE-2020-1845 |
|
Denial of Service |
Huawei Smartphone |
CVE-2019-5303 |
|
Denial of Service |
Huawei Smartphone |
CVE-2019-5302 |
|
Information Disclosure |
IBM Cloud App Management API Stack-based |
CVE-2019-4751 |
|
CSRF |
IBM Cloud App Management |
CVE-2019-4750 |
|
Information Disclosure |
IBM Cognos Analytics Error Message |
CVE-2019-4729 |
|
Information Disclosure |
IBM Maximo Anywhere |
CVE-2019-4288 |
|
Information Disclosure |
IBM Maximo Anywhere |
CVE-2019-4286 |
|
Denial of Service |
IBM MQ/MQ Appliance Memory Leak |
CVE-2020-4267 |
|
Information Disclosure |
IBM WebSphere Application Server/Liberty |
CVE-2020-4329 |
|
Privilege Escalation |
IntelMQ Manager Backend |
CVE-2020-11016 |
|
XSS |
jQuery html() |
CVE-2020-11023 |
|
XSS |
jQuery html() |
CVE-2020-11022 |
|
Privilege Escalation |
JSON Gem Object |
CVE-2020-10663 |
|
SQL Injection |
LearnPress Plugin |
CVE-2020-6010 |
|
XSS |
Lexmark Printer |
CVE-2020-10094 |
|
XSS |
Lexmark Pro910 Inkjet |
CVE-2020-10093 |
|
Privilege Escalation |
LG Bridge DLL |
CVE-2019-20781 |
|
Code Execution |
libgit2 Cloning path.c |
CVE-2020-12278 |
|
Code Execution |
libgit2 Repository Cloning checkout.c |
CVE-2020-12279 |
|
Denial of Service |
libvirt qemu_driver.c qemuDomainGetStatsIOThread |
CVE-2020-12430 |
|
Memory Corruption |
Linux Kernel dma.c mt76_add_fragment |
CVE-2020-12465 |
|
Memory Corruption |
Linux Kernel message.c usb_sg_cancel |
CVE-2020-12464 |
|
Memory Corruption |
Linux Kernel uaccess.c enable_sacf_uaccess |
CVE-2020-11884 |
|
Privilege Escalation |
MonoX ASPX Template |
CVE-2020-12470 |
|
Privilege Escalation |
MonoX ffmpeg.exe |
CVE-2020-12473 |
|
Code Execution |
MonoX HTML5Upload.ashx |
CVE-2020-12471 |
|
XSS |
MonoX Stored |
CVE-2020-12472 |
|
Weak Encryption |
Moonlight Man-in-the-Middle |
CVE-2020-11024 |
|
Information Disclosure |
Moxa NPort 5150A Moxa Service |
CVE-2020-12117 |
|
Remote Code Execution |
Mozilla Firefox ESR Intent |
CVE-2020-6828 |
|
Spoofing |
Mozilla Firefox ESR intent://-schemed Address |
CVE-2020-6827 |
|
Privilege Escalation |
Mozilla Firefox Extension |
CVE-2020-6823 |
|
Memory Corruption |
Mozilla Firefox |
CVE-2020-6826 |
|
Information Disclosure |
Mozilla Firefox Private Browsing Password |
CVE-2020-6824 |
|
Memory Corruption |
Mozilla Firefox/Firefox ESR/Thunderbird |
CVE-2020-6825 |
|
Memory Corruption |
Mozilla Firefox/Firefox ESR/Thunderbird Out-of-Bounds |
CVE-2020-6822 |
|
Information Disclosure |
Mozilla Firefox/Firefox ESR/Thunderbird WebGL Uninitialized Memory |
CVE-2020-6821 |
|
Memory Corruption |
Netgear D3600/D6000/D6100/R6100 |
CVE-2018-21217 |
|
Memory Corruption |
Netgear D3600/D6000/D6100/R6100 |
CVE-2018-21216 |
|
Memory Corruption |
Netgear D3600/D6000/R9000 |
CVE-2018-21221 |
|
Memory Corruption |
Netgear D6100 Stack-based |
CVE-2018-21192 |
|
Memory Corruption |
Netgear D6100/D7800/R7500v2/R7800/R9000 Stack-based |
CVE-2018-21184 |
|
Command Injection |
Netgear D6100/R6100/R7500v2/WNDR4300v2/WNDR4500v3 |
CVE-2018-21208 |
|
Memory Corruption |
Netgear D6100/R7800/R9000/WNDR3700v4/WNDR4300 Stack-based |
CVE-2018-21171 |
|
Command Injection |
Netgear D7800/DM200/R6100/R7500/R7500v2/R7800 |
CVE-2018-21154 |
|
Memory Corruption |
Netgear D7800/R6100/R7500/R7500v2/R7800/R9000/WNDR4300 Stack-based |
CVE-2018-21199 |
|
Memory Corruption |
Netgear EX2700/R7800/WN2000RPTv3/WN3000RPv3/WN3100RPv2 Stack-based |
CVE-2018-21170 |
|
Weak Authentication |
Netgear JNR1010v2/JWNR2010v5/WNR1000v4/WNR2020/WNR2050 |
CVE-2018-21226 |
|
Privilege Escalation |
Netgear R6100 Configuration |
CVE-2018-21231 |
|
Privilege Escalation |
Netgear R6100 Configuration |
CVE-2018-21230 |
|
Information Disclosure |
Netgear R7500v2/R7800/WN3000RPv3/WNDR4300v2/WNDR4500v3 |
CVE-2018-21229 |
|
Command Injection |
Netgear R7800 |
CVE-2018-21100 |
|
Command Injection |
Netgear R7800 |
CVE-2018-21099 |
|
Command Injection |
Netgear R7800 |
CVE-2018-21098 |
|
Privilege Escalation |
Netgear R7800 Configuration Setting |
CVE-2018-21158 |
|
Memory Corruption |
Netgear R7800/R9000 Stack-based |
CVE-2018-21200 |
|
Memory Corruption |
Netgear R7800/R9000/WNDR3700v4/WNDR4300 Stack-based |
CVE-2018-21183 |
|
Memory Corruption |
Netgear R7800/R9000/WNDR3700v4/WNDR4300 Stack-based |
CVE-2018-21182 |
|
Command Injection |
Netgear R9000 |
CVE-2018-21225 |
|
Privilege Escalation |
Netgear ReadyNAS Configuration Setting |
CVE-2018-21159 |
|
XSS |
Netgear SRR60/SRS60 Stored |
CVE-2018-21095 |
|
Memory Corruption |
Netgear WN3100RPv2 |
CVE-2018-21215 |
|
Memory Corruption |
Netgear WN3100RPv2 |
CVE-2018-21214 |
|
Privilege Escalation |
Netgear WN604 Configuration Setting |
CVE-2018-21094 |
|
CSRF |
Netgear WN604 |
CVE-2018-21096 |
|
Memory Corruption |
Netgear WND930 Stack-based |
CVE-2018-21097 |
|
Command Injection |
Netgear WNDR4500v3 |
CVE-2018-21157 |
|
Command Injection |
Netgear WNDR4500v3 |
CVE-2018-21152 |
|
Command Injection |
Netgear WNDR4500v3 |
CVE-2018-21228 |
|
Command Injection |
Netgear WNDR4500v3 |
CVE-2018-21227 |
|
Memory Corruption |
Netgear WNDR4500v3 |
CVE-2018-21213 |
|
Memory Corruption |
Netgear WNDR4500v3 |
CVE-2018-21212 |
|
Memory Corruption |
Netgear WNDR4500v3 |
CVE-2018-21210 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21207 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21206 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21205 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21204 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21203 |
|
Memory Corruption |
Netgear WNDR4500v3 Stack-based |
CVE-2018-21202 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21224 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21223 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21222 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21220 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21219 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21218 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21211 |
|
Memory Corruption |
Netgear WNR2000v5 |
CVE-2018-21153 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21201 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21198 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21197 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21196 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21195 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21194 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21193 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21191 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21190 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21189 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21188 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21187 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21186 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21185 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21181 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21180 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21179 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21178 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21177 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21176 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21175 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21174 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21173 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21172 |
|
Memory Corruption |
Netgear WNR2000v5 Stack-based |
CVE-2018-21149 |
|
XSS |
Netgear WNR2000v5 Stored |
CVE-2018-21167 |
|
XSS |
Netgear WNR2000v5 Stored |
CVE-2018-21155 |
|
Privilege Escalation |
Netgear WNR2050 Configuration Setting |
CVE-2018-21169 |
|
Information Disclosure |
Netgear WNR2050 |
CVE-2018-21168 |
|
XSS |
Netgear WNR2050 Reflected |
CVE-2018-21209 |
|
Memory Corruption |
Netgear WNR3500Lv2 |
CVE-2018-21156 |
|
Memory Corruption |
Netgear WNR3500Lv2 Stack-based |
CVE-2018-21093 |
|
Command Injection |
node-rules fromJSON() |
CVE-2020-7609 |
|
SQL Injection |
Online Course Registration change-password.php |
CVE-2020-12429 |
|
XSS |
Open-AudIT |
CVE-2020-12261 |
|
Privilege Escalation |
Open-AudIT Discovery OS |
CVE-2020-11941 |
|
Privilege Escalation |
Open-AudIT exec |
CVE-2020-12078 |
|
Privilege Escalation |
Open-AudIT File Upload |
CVE-2020-11943 |
|
SQL Injection |
Open-AudIT |
CVE-2020-11942 |
|
Privilege Escalation |
OpenDMARC pypolicyd-spf |
CVE-2019-20790 |
|
Privilege Escalation |
OpenDMARC SPF/DKIM |
CVE-2020-12272 |
|
Denial of Service |
OpenLDAP slapd filter.c |
CVE-2020-12243 |
|
Memory Corruption |
OpenSC card-coolkey.c coolkey_free_private_data |
CVE-2019-20792 |
|
Privilege Escalation |
Openshift Container Platform Man-in-the-Middle |
CVE-2020-1741 |
|
Memory Corruption |
OpenThread GeneratePskc |
CVE-2019-20791 |
|
Privilege Escalation |
OpenVPN Data Channel Injection |
CVE-2020-11810 |
|
Privilege Escalation |
Oracle VM VirtualBox |
CVE-2020-2575 |
|
Information Disclosure |
OTRS Certificates Download |
CVE-2020-1774 |
|
XSS |
PEGA Platform ActionStringID |
CVE-2020-8774 |
|
XSS |
PEGA Platform Comment Tag Stored |
CVE-2020-8775 |
|
XSS |
PEGA Platform Text Editor Stored |
CVE-2020-8773 |
|
Information Disclosure |
Percona XtraBackup |
CVE-2020-10997 |
|
unknown vulnerability |
Percona XtraDB Cluster SST Process |
CVE-2020-10996 |
|
XSS |
pfSense diag_ping.php |
CVE-2020-10797 |
|
Memory Corruption |
PHP EBCDIC Support urldecode() |
CVE-2020-7067 |
|
XSS |
php-fusion Event banners.php |
CVE-2020-12438 |
|
SQL Injection |
php-fusion maincore.php |
CVE-2020-12461 |
|
Privilege Escalation |
pixl-class create |
CVE-2020-7640 |
|
Spoofing |
Postfix sender_login |
CVE-2020-12063 |
|
Denial of Service |
QEMU ATI VGA Emulation ati-2d.c ati_2d_blt() |
CVE-2020-11869 |
|
Memory Corruption |
Qt setMarkdown insertBlock |
CVE-2020-12267 |
|
Weak Authentication |
Rukovoditel Base64 Encoding |
CVE-2020-11821 |
|
Privilege Escalation |
Rukovoditel Maintenance Mode File Upload |
CVE-2020-11817 |
|
XSS |
Rukovoditel User Access Groups Page Stored |
CVE-2020-11822 |
|
Directory Traversal |
SaltStack Salt ClearFuncs |
CVE-2020-11652 |
|
Privilege Escalation |
SaltStack Salt ClearFuncs |
CVE-2020-11651 |
|
Privilege Escalation |
SAP ERP/S-4 HANA Tax Report Clearing |
CVE-2020-6212 |
|
XSS |
SAP NetWeaver AS ABAP SBSPEXT_PHTMLB Reflected |
CVE-2020-6213 |
|
Denial of Service |
SHAREit Body Length |
CVE-2019-14941 |
|
Denial of Service |
SHAREit Message Length |
CVE-2019-15234 |
|
SQL Injection |
Sophos SFOS Administration Service/User Portal |
CVE-2020-12271 |
|
Weak Authentication |
Sourcegraph redirect.go SafeRedirectURL |
CVE-2020-12283 |
|
Privilege Escalation |
SQLiteODBC sqliteodbc$ |
CVE-2020-12050 |
|
Privilege Escalation |
Subrion CMS blocks.php |
CVE-2020-12469 |
|
Privilege Escalation |
Subrion CMS |
CVE-2020-12468 |
|
Weak Authentication |
Subrion CMS Session Fixation |
CVE-2020-12467 |
|
Information Disclosure |
TeamPass |
CVE-2020-12478 |
|
Privilege Escalation |
TeamPass REST API getIp |
CVE-2020-12477 |
|
Directory Traversal |
TeamPass users.queries.php |
CVE-2020-12479 |
|
unknown vulnerability |
Telegram/Telegram Desktop URL |
CVE-2020-12474 |
|
Privilege Escalation |
thinx-device-api IoT Device Management Server MAC Address |
CVE-2020-11015 |
|
Denial of Service |
Tika OneNote Parser Memory Exhaustion |
CVE-2020-9489 |
|
Directory Traversal |
Tiny File Manager Ajax |
CVE-2020-12102 |
|
Privilege Escalation |
Tiny File Manager Ajax File Copy |
CVE-2020-12103 |
|
Memory Corruption |
Ubuntu Linux Overlayfs/shiftfs call_mmap() |
CVE-2019-15794 |
|
Information Disclosure |
Ubuntu Linux shiftfs |
CVE-2019-15793 |
|
Memory Corruption |
Ubuntu Linux shiftfs shiftfs_btrfs_ioctl_fd_replace() |
CVE-2019-15791 |
|
Privilege Escalation |
Ubuntu Linux shiftfs shiftfs_btrfs_ioctl_fd_replace() |
CVE-2019-15792 |
|
Privilege Escalation |
Undertow AJP Connector File Inclusion |
CVE-2020-1745 |
|
Directory Traversal |
UPS Adapter CS141 |
CVE-2020-11420 |
|
Privilege Escalation |
Valve Source Engine hl2_relaunch |
CVE-2020-12242 |
|
XSS |
VMware ESXi Virtual Machine Attribute Viewer |
CVE-2020-3955 |
|
Weak Authentication |
Wagtail String Comparison Timing |
CVE-2020-11037 |
|
Privilege Escalation |
WAVLINK WL-WN579G3/WL-WN575A3/WL-WN530HG4 Wireless Network live_(string).shtml |
CVE-2020-12266 |
|
Memory Corruption |
Wind River VxWorks FTP Client Library Double-Free |
CVE-2020-10647 |
|
Denial of Service |
Wind River VxWorks IGMP NULL Pointer Dereference |
CVE-2020-10664 |
|
XSS |
WordPress Block Editor |
CVE-2020-11030 |
|
XSS |
WordPress class-wp-object-cache.php stats() |
CVE-2020-11029 |
|
XSS |
WordPress Media Section |
CVE-2020-11026 |
|
XSS |
WordPress Navigation Section |
CVE-2020-11025 |
|
Weak Authentication |
WordPress Password Reset Link |
CVE-2020-11027 |
|
Information Disclosure |
WordPress Private Post |
CVE-2020-11028 |
|
XSS |
Zoom International Call Recording Stored |
CVE-2019-18223 |
|
Information Disclosure |
ZTE OSCP |
CVE-2020-6865 |
|
Memory Corruption |
ZTE ZENIC ONE R22b SDON Controller |
CVE-2020-6867 |
|
Denial of Service |
ZTE ZXCTN 6500 Ressource Management |
CVE-2020-6866 |
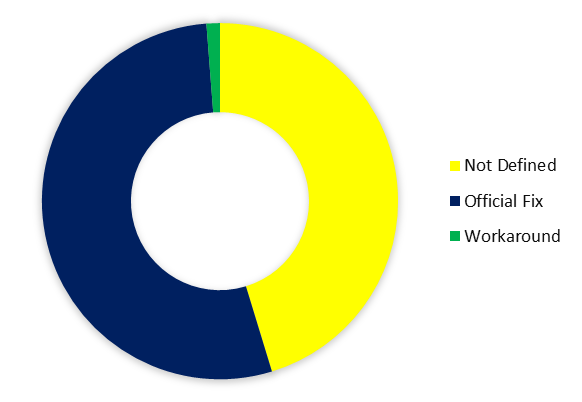
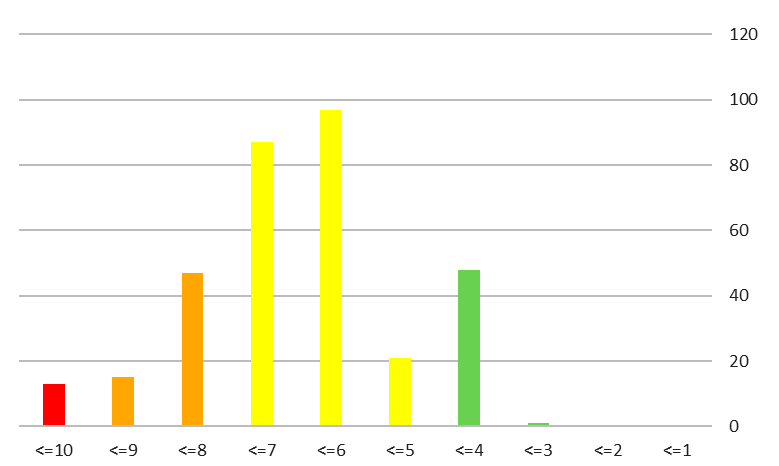
بیشتر آسیبپذیریهای هفته طبق استاندارد CVSS، «خطرناک» ارزیابی شدهاند.
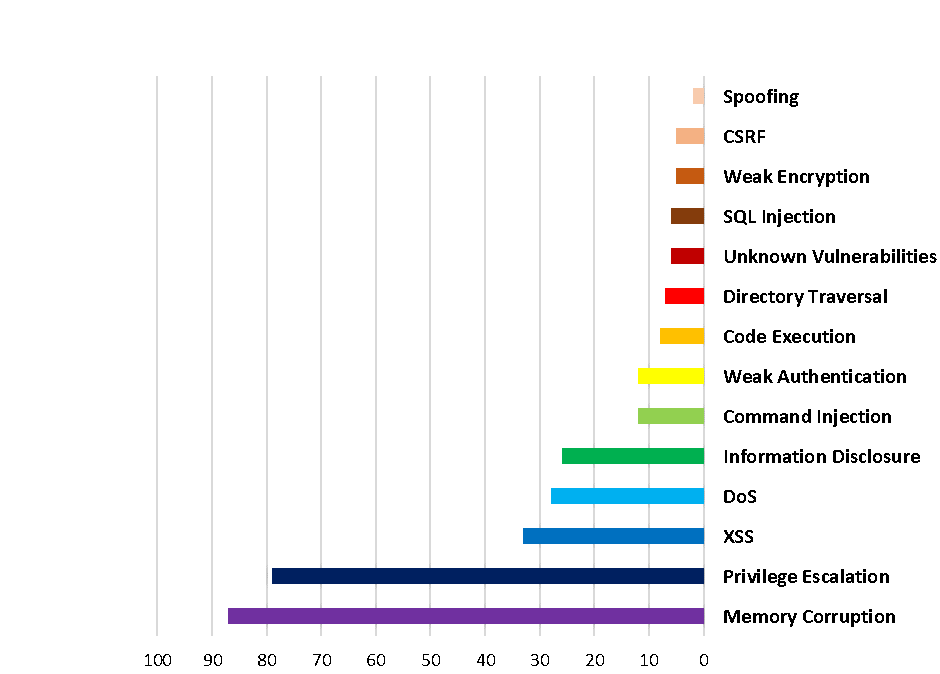
همچنین بیشترین آسیبپذیریهای هفته از نوع تخریب حافظه (۲۷%) و ارتقاء امتیاز (۲۵%) بودند.